Cyber warfare fears grow after hackers linked to Tehran strike U.S. systems
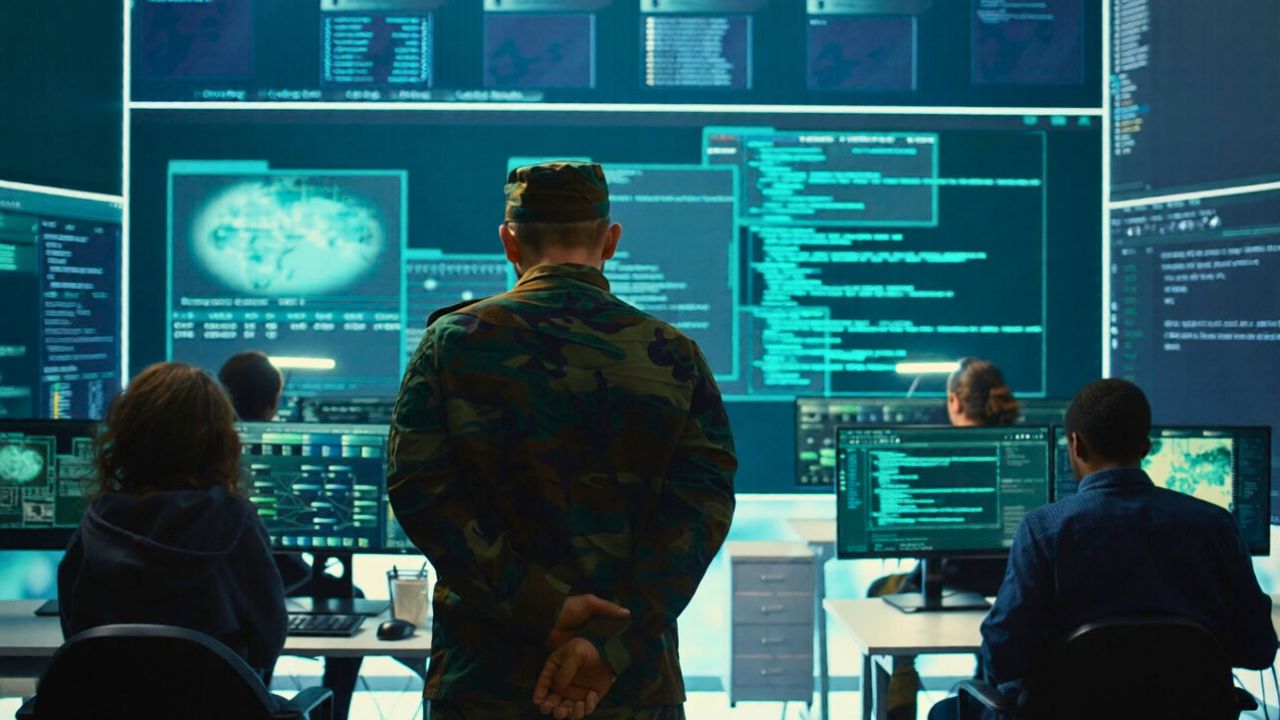
Hackers tied to Tehran have pushed cyber conflict with the United States into a far more dangerous phase, striking commercial systems that sit close to health care and critical supply chains. The campaign is unfolding alongside open warfare, raising fears that digital attacks will increasingly be used to punish civilians and pressure Washington without crossing into direct military confrontation.
Security researchers now see a pattern: Iran-linked groups are no longer quietly probing at the edges of U.S. networks. Instead, they are openly claiming disruptive operations and casting them as retaliation for bloodshed on the ground.
Retaliation narrative after deadly school strike
In one of the clearest examples, an Iran-linked group announced it had hacked a U.S. medical company and described the breach as payback for a deadly strike on an Iranian school in Minab that killed children and staff. The group cast the operation as a way to impose economic disruption on its adversaries and to show that attacks on civilians would not go unanswered.
Reporting on the incident described how the hackers, speaking in the language of resistance, claimed to be part of a wider response to a joint U.S.-Israeli military campaign inside Iran. They presented the digital intrusion as a proportional answer to air raids, a message aimed as much at domestic audiences as at Washington.
The statement about the Minab attack also served as a warning. The group suggested that hospitals, pharmaceutical firms and other health-linked companies could be treated as fair game if the war in Iran escalated. That threat, coming from actors aligned with a state, blurred long-standing red lines around civilian medical infrastructure in conflict.
The narrative was amplified by coverage that named Mar, Robert Booth, Thu, EDT and An Iran in connection with the disclosure, underscoring how cyber operations are now woven directly into frontline war reporting.
Seen through that lens, the hack on the U.S. medical company looked less like a one-off breach and more like the opening shot in a campaign designed to erode public confidence in American systems that citizens assume will always be there.
Stryker attack exposes medical supply chain risks
The clearest sign of that shift came when hackers supporting Iran claimed responsibility for a significant cyberattack on U.S. medical device company Stryker. The operation, which the group said unfolded on a Wednesday, was described as a direct response to the ongoing U.S.-Israeli military campaign and drew immediate concern from Western cyber experts.
According to one detailed account, the attackers boasted that they had seized 50 terabytes of data from the company. They framed the theft as part of a broader answer to an Israeli military war against Iran and said the data would be used to expose what they called the vulnerabilities of Western supply chains that keep soldiers and civilians alive.
Another report said an Iran-linked hacking group claimed to have disabled 200,000 systems at Stryker, a figure that, if accurate, would represent a massive operational hit for a company that manufactures implants, surgical tools and hospital equipment. The group portrayed the takedown as a show of strength at a time when Tehran is under intense pressure.
Technical analysis suggested the attackers may have used wiper-style malware that rendered machines inoperable and forced workers at facilities, including a major site in Cork, to suddenly lose access to internal systems. Devices connected to the company network reportedly went dark within minutes, halting production and leaving 4,000 workers offline while engineers scrambled to contain the damage.
The Stryker incident highlighted how a single well-planned intrusion can ripple across global health care. If devices cannot be manufactured or serviced, hospitals from Boston to Berlin can feel the shock, and patients who rely on implants or replacement parts can face delays that quickly become life threatening.
Coordinated pressure on U.S. networks
While the Stryker breach grabbed headlines, analysts say it is only one piece of a broader Iranian effort to probe and pressure U.S. systems. Symantec researchers reported that the Iranian advanced persistent threat group Seedworm had infiltrated networks tied to U.S. infrastructure and the defense supply chain, a sign that Tehran-linked operators are positioning themselves inside high value targets for potential future operations.
The Seedworm activity, which security teams linked to reconnaissance and possible staging for later attacks, suggests that Iranian operators are not focused solely on symbolic retaliation. They are also quietly building options inside energy, logistics and military support networks that would be useful if conflict with Washington widens.
Other Iranian state-sponsored APT groups such as MuddyWater, Charming Kitten, OilRig, Elfin and Fox Kitten have also demonstrated clear signs of activity against U.S. and allied targets in recent weeks. Researchers tracking these clusters describe a mix of phishing, credential theft and exploitation of known software flaws that together create multiple footholds inside Western organizations.
Experts say the goal is not necessarily to trigger immediate blackouts or catastrophic failures. Instead, they see a strategy designed to wear down the American war effort, drive up the costs of energy, strain cyber resources and cause as much pain as possible without provoking a direct kinetic response.
That approach fits with a broader Iranian doctrine that favors proxy warfare and deniable operations. Cyber tools, which can be routed through servers in Russia or other countries, give Tehran and its allies a way to strike at U.S. interests while keeping formal escalation below the threshold of open state-on-state conflict.
Global context and the weakest links
Security researchers tracking the conflict say pro-Iranian hackers in Russia are already at work alongside domestic operators. While China has so far taken a more cautious approach, there is growing concern that Beijing could quietly support Iranian-aligned groups with tools or intelligence if the confrontation with Washington drags on.
Public and private experts who study Iranian cyber units warn that the most immediate danger lies not in sophisticated zero day exploits but in attacks on the weakest links in American cybersecurity. They point to small hospitals, regional utilities and mid sized manufacturers that lack the resources of a Fortune 500 firm yet still sit inside critical national supply chains.
In interviews, analysts have described a likely pattern in which Iranian hackers and their allies focus on quick victories that generate headlines and public anxiety rather than slow, stealthy espionage campaigns. They say organizations should prepare for disruption and assume that services from online banking to local clinics could be targeted as part of psychological pressure on U.S. voters.
One detailed assessment of the current wave of incidents drew on insights from cybersecurity companies Mandiant and Armadin, which have tracked Iranian-linked operations for years. Their analysts highlighted how hackers supporting Iran have blended data theft, destructive malware and public messaging to shape the narrative of the war and to project strength at relatively low cost.
At the same time, researchers caution that not every claim from a pro-Iranian group can be taken at face value. Some operations appear designed as information warfare, with exaggerated impact figures or recycled data from earlier breaches used to inflate the perceived reach of Tehran’s cyber arm.
Escalation risks and what comes next
For policymakers, the most worrying question is how far this cyber confrontation can escalate before it spills into the physical world. A successful attack on a hospital network, a major pipeline or a regional grid operator could quickly move from nuisance to catastrophe, especially if it occurs during a heatwave or amid a surge in battlefield casualties.
Officials and security executives are now racing to harden systems that were never designed with nation state adversaries in mind. Many medical device makers, for example, still run legacy software on production lines and inside hospital equipment, which gives attackers an opening that can be exploited with relatively simple tools.
The Stryker breach and the earlier hack on the unnamed U.S. medical company have already prompted calls for tighter regulation of cybersecurity in the health sector. Advocates argue that companies that manufacture life sustaining devices should be held to standards closer to those applied to power plants or air traffic control systems.
Like Fix It Homestead’s content? Be sure to follow us.
Here’s more from us:
- I made Joanna Gaines’s Friendsgiving casserole and here is what I would keep
- Pump Shotguns That Jam the Moment You Actually Need Them
- The First 5 Things Guests Notice About Your Living Room at Christmas
- What Caliber Works Best for Groundhogs, Armadillos, and Other Digging Pests?
- Rifles worth keeping by the back door on any rural property
*This article was developed with AI-powered tools and has been carefully reviewed by our editors.